Create a Twitter App
Several of the following workshops involve the Twitter API to supply content and demonstrate a real world scenario. Twitter supports a number of APIs that all require a developer to register an application and collect some credentials. You’ll need to create a regular twitter account before creating a twitter app.
Step 1. Create a Twitter App
Navigate to https://developer.twitter.com/en/apps and signin with your twitter account (or create a twitter account).
Select “Create an app” in the top right corner.

Now fill out the “App details” form.
- App name (required) - this should be a unique name related to this workshop so you can recognize it later.
- Application description (required) - this should be a brief description of the application over 100 characters. Something like “This is a demonstration application used to learn the Twitter API with AWS tools.”
- Website URL (required) - for now you can put in a personal site or https://ai-services.go-aws.com/ - other workshop may require you to change this.
- Tell us how this app will be used (required) - here you need to explain to twitter that this is a demonstration application used to explore the twitter API and AWS AI APIs.

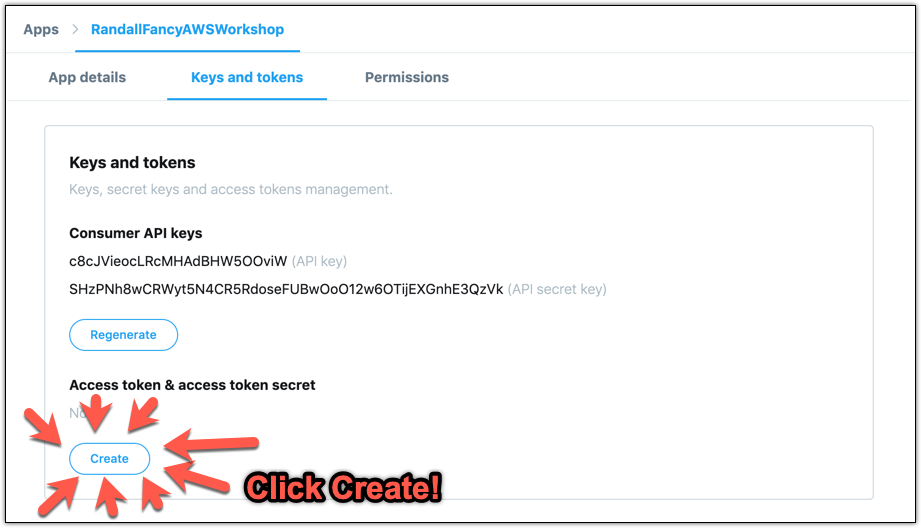
After the app is created click on the “Keys and tokens” tab.

The first two keys listed on this page are generated by Twitter and are specific to your application. They’re the first half of the credentials used to make requests to Twitter and many requests can be made with just the application credentials. The second half of the credentials are specific to your twitter user (or whoever is using your application). Combined the two credentials let you make requests as your application on behalf of your user.
This authorization and authentication model is often called OAuth and it's pretty standard for APIs across the web.For now, Twitter’s developer portal provides a convinient method for authenticating your own twitter user to the application you just created by clicking “Create” under “Access token & access token secret”
 Keep these credentials secret. Do not publish them publically.
Keep these credentials secret. Do not publish them publically.Now we’ll want to take down these credentials somewhere safe for use later in the lab.

From here you should be ready to start any of the workshops!